In many cases, scammers impersonate banks, technology companies, government agencies, or customer support teams to pressure people into sharing sensitive information or sending money.
These operations rely heavily on social engineering tactics, such as urgency or authority, combined with techniques like caller ID spoofing to make calls appear legitimate.
In this guide, we break down how call center scams work, the most common fraud scenarios used today, and how to recognize suspicious calls before they lead to financial or data loss.
What a call center scam actually looks like today
Many modern phone scams operate more like organized contact centers than isolated fraud attempts. Instead of a single caller, these operations often involve teams using VoIP systems, automated dialers, and call routing tools to place large volumes of calls.
To appear legitimate, scammers frequently use caller ID spoofing, allowing them to display the phone numbers of banks, government agencies, or technology companies. Agents typically follow prepared scripts and may track targets using simple CRM-style tools or spreadsheets.
This structure allows fraud groups to run scams at scale and train agents in social engineering techniques designed to pressure victims into sharing sensitive information or sending money.
These schemes are commonly known as vishing (voice phishing): a form of phishing carried out through phone calls instead of emails or messages. Unlike traditional one-off phone scams, modern call center fraud relies on organized teams, technology infrastructure, and repeatable scripts to increase success rates.
Why call center scams work so well
Modern call center scams are effective because they combine telecommunications technology with structured social engineering tactics designed to guide victims toward specific actions.
Social engineering scripts designed for pressure
Scam call centers typically rely on structured scripts rather than improvised conversations. These scripts are designed to move the target through a predictable sequence.
First, the caller establishes authority, often claiming to represent a bank, government office, or technology company. Next comes urgency, such as warning about suspicious transactions, security breaches, or legal consequences.
The caller then offers a solution, such as verifying an account, reversing a charge, or fixing a technical issue. The final step is payment or information extraction, where the victim is asked to provide verification codes, banking details, or remote access to a device.
In many cases, these interactions overlap with identity theft or phishing attempts, where the real objective is to collect credentials or personal data that can be used later.
Caller ID spoofing and trust hijacking
Caller ID spoofing plays a major role in making scam calls appear legitimate. Using VoIP routing tools, scammers can manipulate the number displayed on a recipient’s phone so it matches a trusted organization.
This allows fraudsters to impersonate banks, government offices, or technology support lines, even if the call is originating from another country. Some scams also use local number impersonation, where the displayed number appears to come from the recipient’s area code, increasing the likelihood that the call will be answered.
Multi-channel fraud: combining phone, email, and SMS
Scammers combine several communication channels to build credibility before speaking to the victim.
A common sequence starts with a phishing email, followed by an SMS alert warning about suspicious activity. Shortly afterward, the victim receives a call from someone claiming to be from a bank’s fraud department.
By the time the phone call happens, the target may already believe the situation is legitimate. This combination of email, messaging, and voice communication has become a common tactic in recent fraud operations.
The most common call center scams targeting people today
Most call center scams follow repeatable playbooks. Fraud operations train agents to follow structured scripts that guide victims toward sharing sensitive information, granting device access, or sending money. While the story may change, the mechanics behind these scams tend to follow the same patterns.
Tech support scams
In tech support scams, callers impersonate well-known technology companies such as Microsoft, Apple, or antivirus providers.
How it works: The caller claims the victim’s device is infected with malware or has been hacked. They offer to “fix” the issue by guiding the victim through diagnostic steps.
What scammers ask for: Victims are often asked to install remote desktop software, allowing the caller to control the device. From there, scammers may request payment for fake repairs or install malicious software.
Warning signs: Legitimate tech companies do not make unsolicited calls about device problems, and unexpected requests for remote access should be treated as suspicious.
Bank impersonation and financial fraud calls
These scams involve callers posing as representatives from a bank’s fraud department.
How it works: The victim is told there has been a suspicious transaction or security issue with their account.
What scammers ask for: Scammers attempt to collect one-time passcodes (OTPs), account passwords, or card details, often claiming they are needed to verify or cancel the transaction.
Warning signs: Calls may appear to come from a spoofed bank phone number, and the caller typically pressures the victim to act quickly.
Government or tax authority scams
Fraudsters frequently impersonate tax agencies, immigration offices, or law enforcement authorities.
How it works: The caller claims the victim owes unpaid taxes, has an immigration issue, or faces legal action.
What scammers ask for: Victims are instructed to make immediate payments, sometimes through wire transfers, gift cards, or cryptocurrency.
Warning signs: Strong pressure to pay immediately and threats of arrest or legal action are common indicators of this type of scam.
Refund and subscription cancellation scams
These scams revolve around false claims about refunds for services or subscriptions.
How it works: The caller says the victim is owed a refund for a cancelled service or overpayment.
What scammers ask for: Victims are often asked to grant screen-sharing or remote access so the caller can “process” the refund. During this process, scammers may manipulate online banking screens or trick the victim into transferring funds.
Warning signs: Unexpected refund calls combined with requests for device access or banking login steps are a common red flag.
Charity and disaster donation scams
Fraudsters often exploit major disasters, crises, or humanitarian events.
How it works: Callers claim to represent charities collecting donations for relief efforts.
What scammers ask for: They request immediate donations, sometimes directing victims to payment methods that are difficult to trace.
Warning signs: Unverified organizations, urgent donation requests, and limited information about the charity should raise concern.
Prize and lottery scams
These scams target victims with claims that they have won a prize or lottery.
How it works: The caller informs the victim that they have won money or a valuable prize.
What scammers ask for: Victims are told they must first pay taxes, processing fees, or release charges before the prize can be delivered.
Warning signs: Requests for upfront payments and claims about prizes from contests the victim never entered are typical signs of this scam. These schemes frequently target older adults, who may be more likely to receive repeated follow-up calls.
How professional scam call centers operate
Many large-scale phone scams are run as organized operations rather than individual fraud attempts. These groups often mirror the structure of legitimate outsourced contact centers, using agents, scripts, and telecommunications systems to handle high volumes of calls.
Fake BPO-style operations
Some fraud rings operate from offices that resemble business process outsourcing (BPO) call centers. Agents may receive training on specific scam scripts, how to handle objections, and how to guide victims toward payment or information disclosure.
Callers typically follow standardized scripts and may work toward daily targets, similar to sales teams. In some operations, agents are paid commissions or bonuses based on successful scams. Law enforcement investigations in several regions, including parts of South Asia and Eastern Europe, have uncovered organized fraud centers running these types of operations.
The technology stack scammers use
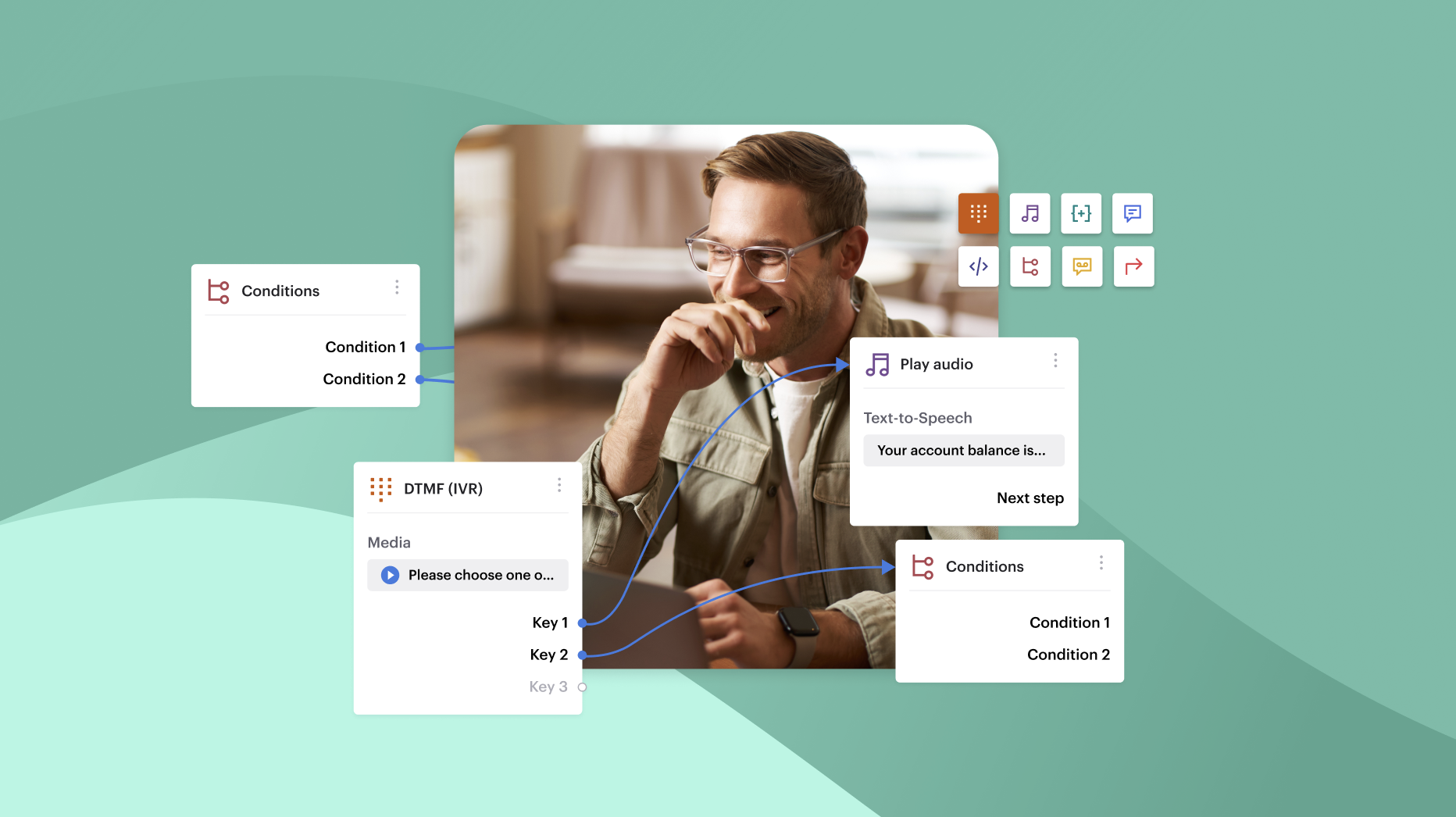
Scam call centers often rely on inexpensive cloud communication tools that are widely available online.
Common tools include VoIP dialers, robocall systems, and software that allows caller ID spoofing. These systems can place thousands of calls quickly and route answered calls to available agents.
Some operations also track potential victims using CRM-style dashboards or spreadsheets, allowing agents to record previous interactions and schedule follow-up calls. Combined with automated call routing, these tools allow fraud groups to manage their activity at scale.
Lead generation for scam calls
To sustain large calling operations, scammers need access to large lists of phone numbers and personal data.
These lists can come from several sources, including leaked databases, phishing campaigns, and information purchased from data brokers or dark web marketplaces. Once acquired, the data is often organized into calling lists so agents can prioritize targets who may be more likely to respond.
Red flags that reveal a call center scam
While scam scripts vary, many fraudulent calls follow similar behavioral patterns. Recognizing these warning signs can help individuals identify suspicious calls before sharing sensitive information or sending money.
Signs during the call
Certain behaviors frequently appear in scam calls.
Callers may refuse verification requests, avoid giving a callback number, or insist that the conversation must continue without interruption. Many also pressure victims to stay on the line while they “resolve” the issue.
Another common tactic is requesting sensitive information such as one-time passcodes (OTPs), account passwords, or banking details. These requests are often framed as necessary to confirm identity or stop fraudulent transactions.
Scammers also rely heavily on urgency, pushing victims to make immediate payments or transfers. In some cases, background noise resembling a busy call center and overly scripted responses can also indicate that the call is part of a coordinated fraud operation.
How to verify a suspicious call safely
If a call seems suspicious, the safest approach is to end the conversation and verify the claim independently.
Start by hanging up immediately rather than continuing the conversation. Then contact the organization directly using the official phone number listed on its website or account documents.
You can also search the number online or check scam-reporting databases to see if others have flagged similar calls. If the call appears fraudulent, report it to relevant consumer protection agencies or telecom providers so the incident can be documented.
How individuals can protect themselves from call center fraud
While scam tactics continue to evolve, a few practical precautions can significantly reduce the risk of falling victim to phone-based fraud.
Use call-screening apps and robocall filters where available. Many mobile devices and telecom providers offer tools that identify or block known spam numbers before the call is answered.
Be cautious about sharing sensitive information over the phone. Never provide one-time passcodes (OTPs), passwords, or full banking details during unsolicited calls, even if the caller claims to represent a legitimate organization.
If a caller claims to be from a bank, government agency, or service provider, verify the request independently. End the call and contact the organization using the official phone number listed on its website or account documentation.
It is also helpful to limit how widely your phone number is shared online. Phone numbers published on websites, directories, or social media can sometimes be collected and added to scam call lists.
Most importantly, remember that legitimate companies and banks typically do not request sensitive account information or verification codes through unexpected calls. Treat any request for this type of information as a strong warning sign.
How businesses can prevent their brand from being used in scams
Phone scammers frequently impersonate well-known companies to increase credibility. When customers receive fraudulent calls that appear to come from a trusted brand, the result can be financial harm for victims and reputational damage for the company being impersonated. Reducing this risk requires both technical controls and clear operational processes.
Caller authentication and verified numbers
One way to reduce impersonation risk is to maintain consistent outbound numbers and clearly document official support channels customers should trust. Define customer verification procedures (for example, asking customers to call back using an official number from your website or statements) so they can confirm they’re speaking with your team.
Track internal call activity and customer-reported scam incidents over time so your team can investigate patterns and publish timely guidance when impersonation campaigns appear to target your brand.
Monitoring abnormal call patterns
Organizations can also watch for patterns that may indicate fraudulent activity linked to their brand. This may include reports of spoofed phone numbers, unusual spikes in customer complaints about scam calls, or suspicious outbound call traffic appearing to originate from numbers associated with the company.
Tracking these signals allows teams to investigate potential impersonation attempts and warn customers when scam campaigns appear to be targeting their brand.
Employee training against social engineering
Internal training also plays an important role in fraud prevention. Customer-facing teams should understand common social engineering tactics and know how to handle suspicious interactions.
This typically includes training on fraud recognition, consistent customer verification procedures, and clear guidelines for secure call handling. Well-defined processes help ensure employees protect sensitive information while maintaining a consistent experience for legitimate customers.
Discover how platforms like Voiso can help teams review call activity and investigate suspicious reports.
FAQs
What is the most common call center scam?
One of the most common scams involves bank or financial service impersonation. A caller claims to be from a bank’s fraud department and warns about a suspicious transaction. The goal is to pressure the victim into sharing one-time passcodes (OTPs), account credentials, or card details, which can then be used to access accounts or authorize payments.
How do scammers spoof phone numbers?
Scammers use VoIP systems and caller ID manipulation tools to display a different phone number than the one actually making the call. This technique, known as caller ID spoofing, allows them to imitate trusted numbers such as banks, government agencies, or local businesses.
What should I do if I gave information to a scammer?
Act quickly. Contact your bank or service provider immediately to report the incident and secure your accounts. Change any compromised passwords and monitor financial activity for unusual transactions. You should also report the scam to local consumer protection or fraud reporting agencies.
Can businesses prevent their numbers from being spoofed?
Preventing spoofing entirely can be difficult because scammers can manipulate caller ID information. However, businesses can reduce risk by maintaining consistent official contact numbers, monitoring customer reports, and working with telecom providers to identify suspicious activity involving their brand.
How can companies protect customers from fraud calls?
Companies can help by clearly communicating official contact channels, training support teams to follow strict verification procedures, and warning customers about common scam tactics. Monitoring customer complaints and providing guidance on how to verify legitimate calls can also reduce the impact of impersonation scams.