That doesn’t mean you’re out of options.
Depending on your carrier, where you live, and the context of the call, you may be able to trace it through your provider, escalate it if it turns into harassment, or verify whether it was a real business trying to reach you. For organizations running contact centers, it’s a different story: internal call logs and routing records often retain metadata even when the caller ID is masked on the outside.
This guide covers what’s technically possible, what isn’t, and what actually makes sense for both personal and business situations. No myths. No workarounds that fall apart on contact. Just the operational reality behind “No Caller ID” calls.
What “No Caller ID” actually means at the network level
When someone places a call, their number travels through the telecom network as part of the signaling data. This identifier is commonly called CLI (Calling Line Identification). If CLI is withheld, the receiving device has no number to display.
Understanding how that suppression works helps clarify what you can and can’t do when you try to call back.
Caller ID suppression vs. “Unknown Number”
Caller ID suppression is when the caller deliberately prevents their number from showing up. In the US, dialing *67 before a number blocks CLI for that call. In the UK, the equivalent is 141. The network still knows the number, but flags it as withheld for the recipient.
Network-level restriction is different. A company using a PBX or VoIP system can configure outbound calls to hide direct agent numbers. Instead of transmitting the individual line, the system might withhold it entirely or present a generic trunk number. Sometimes the CLI gets stripped upstream by the carrier.
These are different from an “Unknown Number.” An unknown number usually shows up when the network can’t deliver CLI at all; maybe because of international routing issues or signaling problems between carriers. The number wasn’t deliberately hidden; it just wasn’t available.
“Private Number” is often used interchangeably with “No Caller ID.” In most cases, it means intentional CLI suppression.
A spoofed number is something else entirely. With spoofing, the caller deliberately sends a fake CLI instead of withholding it. You see a number, but it doesn’t belong to whoever actually placed the call.
Here’s the breakdown:
- No Caller ID / Private Number = CLI intentionally suppressed.
- Unknown Number = CLI unavailable due to routing or network issues.
- Spoofed number = CLI intentionally faked.
In all suppression cases, your phone can’t reveal what was never delivered to it.
Why businesses and individuals hide their caller ID
Hidden numbers aren’t automatically suspicious. In many industries, masking outbound calls is a deliberate policy choice.
Compliance-heavy industries like fintech and credit collections often centralize outbound communication through controlled trunk lines. Agents don’t expose their direct numbers. This limits personal data exposure and keeps communication within monitored systems.
Outbound call centers do the same thing for similar reasons. Calls may come from shared outbound pools rather than individual extensions. The visible caller ID gets withheld or standardized.
Healthcare and legal organizations often suppress direct lines to protect staff. Instead, they route callbacks through main switchboards or case management desks.
VoIP routing can also mess with caller ID visibility. When calls pass through international carriers or multiple SIP trunks, CLI can be restricted, reformatted, or dropped depending on interconnect agreements.
The point: a hidden number doesn’t automatically mean fraud. Plenty of legitimate businesses with structured outbound processes mask caller ID on purpose.
What matters is the intent behind the suppression, not the label on your screen.
Can you call back a No Caller ID number?
No. You can’t directly call back a No Caller ID number.
If the caller suppressed their CLI, your device never received a returnable number. There’s nothing stored on your phone that you can tap or redial. Any solution that assumes the number is hidden “inside” your phone misunderstands how telecom signaling works.
There are narrow edge cases where callback tools work. They depend on carrier infrastructure, timing, and call routing.
When call return codes work (and when they don’t)
Some countries offer call return services through carrier short codes.
In the US and Canada, *69 may try to return the most recent incoming call. In the UK, 1471 gives information about the last caller and may let you call back.
These services only reference the last incoming call. They’re not a call history lookup. Timing matters; you usually need to make the request shortly after the call.
Even then, results vary.
Call return can fail if:
- The caller used carrier-level blocking that prevents callback routing.
- The call came through a VoIP system that doesn’t support automatic return services.
- The call was routed internationally and signaling data was limited or reformatted in transit.
- Your carrier doesn’t support call return in your region or plan.
These codes rely on carrier-side records, not data on your phone. If the carrier can’t complete the return, that’s where it ends.
Why most “reveal No Caller ID” hacks don’t work
Online advice loves to suggest secret dialing codes, special number combinations, or apps that promise to “unmask” private numbers.
In practice, these almost never deliver what they claim.
Random dialing sequences floating around on forums are usually outdated, country-specific, or tied to legacy landline systems. They don’t override network-level suppression.
Third-party apps claiming to reveal hidden numbers typically rely on crowdsourced databases. If a number was never transmitted to your device, there’s no record for an app to pull up.
Some services charge a fee for “instant unmasking.” Be cautious with these. They often either produce nothing or redirect you toward premium-rate numbers.
Reverse lookup tools only work when a number exists. They can’t retrieve what was never delivered.
A practical rule: if the number didn’t show on your screen, no consumer tool can reliably reconstruct it. Most viral advice oversimplifies carrier behavior or assumes capabilities that don’t apply across regions.
Knowing these limits saves you from chasing workarounds that depend on outdated infrastructure, and helps you focus on options that are actually available.
How to identify a No Caller ID caller legally
If a caller intentionally withholds their number, no consumer tool can just “reveal” it. The only legitimate paths run through your carrier and, in more serious cases, law enforcement.
The process is structured. It’s not instant, and it’s not built for curiosity. It exists to deal with harassment, threats, or fraud.
Use carrier call trace (for harassment or fraud)
In the United States, dialing *57 after receiving a call activates a carrier-level call trace. Other countries have similar services under different codes.
You have to do this right after the call ends. The trace doesn’t show you the number. Instead, it creates an internal record in the carrier’s system.
If things escalate, that record can be shared with law enforcement. The purpose is evidentiary, not informational.
A typical escalation path:
- You activate call trace after a problematic call.
- You document the date and time.
- You file a police report if the behavior continues or involves threats.
- Authorities request the relevant records from the carrier.
Carriers won’t give you the traced number directly. The trace exists to support formal investigations.
Contact your mobile carrier
Your carrier keeps call metadata in its internal systems (routing information, timestamps, originating network data) even when CLI is suppressed.
But carriers don’t hand out hidden numbers freely.
Disclosure usually requires one of the following:
- A documented harassment complaint.
- A fraud investigation.
- A formal request from law enforcement.
- A court order or subpoena.
Privacy regulations limit what carriers can share. Under GDPR, CCPA, and other telecom privacy laws, subscriber information is protected personal data. Even if a number exists in internal records, carriers can’t release it without a lawful basis.
If you contact support, have this ready:
- Date and exact time of the call.
- How long the call lasted.
- A description of what happened.
- Screenshots of your call log if you have them.
- Any related voicemail recordings.
Expect the carrier to walk you through their disclosure policy. In many cases, they’ll document your complaint but won’t release identifying details without a formal request.
Timelines vary. Non-urgent cases may take several business days. For active threats, carriers usually direct you to law enforcement right away.
Law enforcement access to hidden numbers
When a call involves threats, stalking, or financial fraud, law enforcement can request carrier records through legal process.
This typically requires:
- A filed police report.
- Clear documentation of repeated incidents.
- Evidence like timestamps, recordings, or messages.
Authorities can subpoena carrier metadata: the originating number, routing path, and associated account details, depending on what the carrier retains.
This process is formal and evidence-driven. It’s not designed for figuring out who called you once. It exists to address harm, risk, or criminal behavior.
If you’re dealing with repeated unwanted contact, keeping clear records improves the odds of meaningful action.
How businesses handle No Caller ID calls
For individuals, a hidden number feels like a dead end. For contact centers, it’s a different situation.
Even when caller ID is suppressed on the receiving device, business phone systems often retain structured metadata about the interaction. What’s visible depends on network configuration and routing, but it’s rarely limited to what the agent sees on screen.
What call centers see even when caller ID is hidden
When a call enters a cloud contact center, it passes through SIP signaling. That signaling can carry multiple identifiers beyond the visible caller ID.
Two terms matter here:
- CLI (Calling Line Identification): the number shown to the recipient.
- ANI (Automatic Number Identification): a network-level identifier used for billing and routing.
In some setups, CLI is withheld while other routing metadata remains available in the signaling headers. In others, both are restricted. What you can see depends on carrier agreements and trunk configuration.
Even when the caller number is masked, contact centers still log structured call data. Modern platforms generate Call Detail Records (CDRs) for every interaction. These records typically include timestamps, routing paths, queue data, and call outcomes, whether or not a number showed up on the agent’s screen.
So a “No Caller ID” call is rarely invisible inside a business system. It’s an interaction with recorded operational context around it.
Using call detail records to investigate anonymous calls
When reviewing an anonymous inbound call, operations teams usually turn to Call Detail Records.
CDRs let teams look at:
- Exact date and time of the call.
- Call duration.
- Queue or IVR path taken.
- Which agent handled the call.
- Wrap-up codes or disposition.
- Whether a recording is available.
- Whether a transcript exists (if speech analytics is active).
Even without a visible number, the interaction can be analyzed in context.
For compliance-heavy industries like fintech or microlending, this structured logging matters operationally. Teams need to:
- Document customer interactions.
- Review disputed conversations.
- Check adherence to internal communication policies.
- Escalate threatening or abusive behavior.
The investigation is less about “who called” and more about “what happened” during the interaction.
AI speech analytics for risk detection
Where speech analytics is enabled, post-call analysis adds another layer of visibility.
Transcripts can be generated from recorded calls. Supervisors can review AI-generated summaries and conversation scores to get context faster.
In practice, this supports:
- Flagging predefined keywords tied to threats or abusive language.
- Spotting recurring patterns across anonymous calls.
- Reviewing sentiment trends at the call level.
- Grouping calls by topic for structured follow-up.
This analysis happens after the call. It doesn’t intervene in real time and doesn’t take automatic action. It gives supervisors structured data to review and decide on next steps.
For organizations handling regulated or sensitive conversations, this combination of CDR data, recordings, and transcript review lets them manage anonymous inbound calls in a controlled and auditable way, even without caller ID.
How to call back safely (if you think it was legitimate)
Not every No Caller ID call is malicious. Many organizations suppress outbound numbers for operational reasons. The question isn’t whether to call back immediately. It’s whether there’s a verified path to return the call safely.
The safest approach: validate the source before you make contact.
Check for voicemail or SMS follow-up
Legitimate businesses rarely rely on a single unanswered call.
In most structured outbound workflows, agents are expected to:
- Leave a voicemail identifying the organization.
- Provide a main callback number.
- Send an SMS confirmation when appropriate.
- Reference a case number, order number, or support ticket.
SMS follow-up is common because open rates are high: industry data often puts SMS open rates near 98%, which makes it a reliable way to confirm a contact attempt.
If a company genuinely needs to reach you, they’ll usually provide an official callback route. That route should point to a published business number, not someone’s direct line.
If there’s no voicemail, no SMS, and no official contact path, caution makes sense.
Verify before you dial
If you think the call might have been legitimate, verify independently before returning it.
Go to the company’s official website and use the number listed there. Don’t rely on a number from an unknown text or voicemail without cross-checking it first.
Check whether the area code matches the organization’s stated location. Keep in mind that VoIP systems allow geographic number masking, so this is a clue, not proof.
Avoid calling back unfamiliar international numbers, especially if you weren’t expecting overseas contact.
Never share one-time passcodes (OTPs), account reset codes, or banking verification codes with someone who contacted you first. Legitimate organizations don’t ask for security codes during an unsolicited outbound call.
Always verify through channels you initiate, not numbers someone pushed to you.
Red flags of callback scams
Certain patterns show up repeatedly in callback fraud.
The “one-ring” scam, often called Wangiri fraud, is a short missed call from an international number. The goal is to get you to call back a premium-rate line that racks up charges.
International premium numbers with unfamiliar country codes are a common risk. If you weren’t expecting international contact, treat it with caution.
Urgency language is another tell. Phrases like “final notice,” “immediate action required,” or “account will be closed today” are designed to create pressure.
Requests for verification codes during a callback are especially worrying. A caller might claim they need to “confirm your identity” and ask you to read back a code sent to your phone. That code is often part of an account takeover attempt.
A practical rule: if you can’t independently confirm the organization and its official contact channel, don’t return the call. Reach out yourself using verified details.
Blocking No Caller ID calls (prevention)
If repeated anonymous calls are disrupting your day, prevention is more practical than tracing.
Blocking works at three levels: device, carrier, and business system configuration. Each comes with trade-offs.
iPhone and Android settings
Both iOS and Android have controls that limit calls from unidentified numbers.
On iPhone, “Silence Unknown Callers” sends calls from numbers not in your contacts straight to voicemail. The call still shows in your recents, but your phone doesn’t ring.
On many Android devices, similar options sit under call settings, often labeled “Block unknown/private numbers” or spam filtering controls.
These settings cut down on interruptions. They don’t stop the call from reaching your carrier network.
There are downsides:
- Legitimate first-time callers get silenced.
- Healthcare providers, banks, or support teams that mask outbound numbers may not get through.
- Emergency callbacks could be affected in some configurations.
Before turning on strict blocking, think about whether you expect contact from organizations that routinely suppress caller ID.
Carrier-level blocking
Most mobile carriers offer spam filtering and call screening services.
These may:
- Label suspected spam calls.
- Filter high-risk traffic.
- Let you block calls that withhold CLI entirely.
Carrier-level blocking is more effective than device settings because it works within the network. But it still can’t perfectly distinguish intent. A blocked private number might belong to a legitimate organization using masked routing.
Permanently blocking all No Caller ID calls makes sense when:
- You don’t expect legitimate masked calls.
- Anonymous calls are persistent and disruptive.
- You’ve confirmed alternative contact paths for important services.
For business-critical lines, permanent blocking is rarely a good idea without additional routing controls.
Business-level controls
Organizations usually manage anonymous inbound traffic through routing logic rather than blanket blocking.
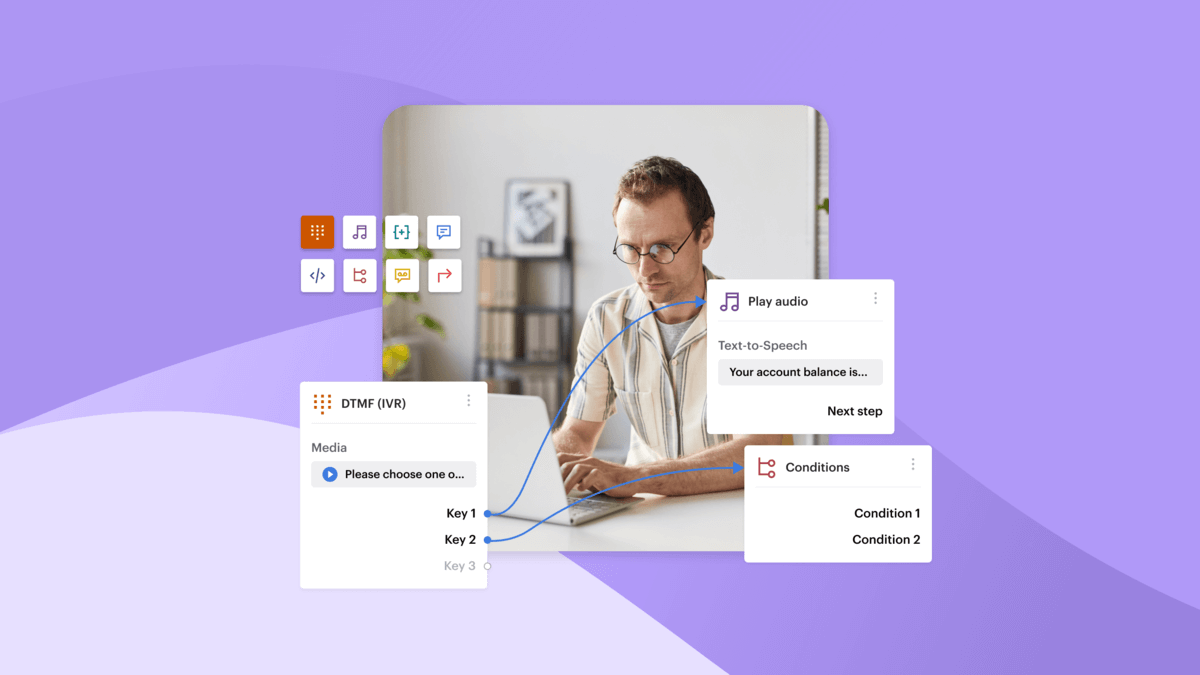
With IVR configuration, businesses can build call flows that screen inbound calls before they reach agents. This might include:
- DTMF prompts requiring the caller to press a key to continue.
- Routing anonymous calls to a dedicated queue.
- Sending withheld numbers to voicemail.
- Offering self-service options before connecting to an agent.
In structured contact center environments, these flows are set up through rule-based routing tools rather than manual intervention. Drag-and-drop IVR builders, for example, let teams define how calls are handled based on specific conditions.
This approach doesn’t try to “unmask” the caller. It controls how anonymous traffic enters the operation.
For many businesses, especially in regulated industries, controlled routing beats outright blocking. It keeps services accessible while maintaining operational guardrails.
Legal and privacy considerations
Tracing or identifying a No Caller ID caller is governed by telecom and data protection law.
The restrictions exist to protect both the caller and the recipient.
Under GDPR and similar privacy frameworks, phone numbers are personal data. Carriers can’t disclose subscriber identity just because a recipient wants to know. Even when the originating number sits in carrier records, releasing it without a lawful basis can violate data protection regulations.
This is why carriers require formal complaints, documented harm, or legal requests before sharing information. Tracing is a regulated process, not a shortcut around anonymity.
Recording laws add another layer.
In one-party consent jurisdictions, only one person on the call needs to know it’s being recorded. In two-party (or all-party) consent jurisdictions, everyone must be told. Businesses operating across regions need to account for these differences when recording anonymous inbound calls.
Payment data brings its own rules. Under PCI DSS requirements, organizations handling cardholder data must protect sensitive information during collection and storage. Many contact centers pause or limit recording during payment capture to reduce exposure. A hidden caller ID doesn’t remove those obligations.
There’s also a line between legitimate tracing and unlawful surveillance. Trying to bypass carrier controls, buying questionable “unmasking” services, or using deceptive tactics to extract identity information can cross legal boundaries fast.
The practical principle: identifying a hidden caller is allowed only through regulated channels. Outside those channels, the risk shifts from nuisance to liability.
When you should escalate
Most anonymous calls are harmless. Escalation makes sense when the behavior crosses into actual risk.
Clear triggers:
- Repeated unwanted contact after you haven’t engaged.
- Explicit threats.
- Attempts to get financial or authentication information out of you.
- Patterns consistent with stalking or intimidation.
- Signs of account takeover attempts.
When escalation is warranted, documentation matters.
Record:
- The exact date and time of each call.
- Call duration.
- Screenshots of your call log.
- Any voicemail content.
- Any related text messages.
Don’t edit recordings. Keep them as received.
What comes next depends on severity.
For nuisance-level repetition, contact your carrier and ask about call trace or formal complaint options.
For threats, fraud, or stalking, file a police report. Bring documented timestamps and any recordings. Authorities can request carrier metadata through legal process if needed.
Escalation should follow a clear path. Anonymous calls are annoying. They become actionable when backed by solid records and formal reporting channels.
How modern contact centers reduce anonymous call risks
Anonymous calls create two operational problems for businesses: wasted outbound effort and uncontrolled inbound traffic.
Modern contact centers don’t try to “unmask” callers. They reduce risk by tightening routing logic, improving channel strategy, and making outbound operations more efficient.
Answering machine detection (outbound context)
In outbound operations, a big chunk of calls never reach a live person. Industry data commonly cited in dialer documentation puts it at up to 78% of outbound campaign calls reaching voicemail.
Without filtering, agents burn time waiting through greetings or manually classifying outcomes. That drags on productivity and muddies reporting.
Answering Machine Detection (AMD) uses AI models to tell human pickups from machine responses before connecting the call to an agent. When configured, only calls identified as live answers get routed to agents.
This doesn’t eliminate voicemail entirely. It cuts wasted talk time and keeps outbound teams focused on actual conversations.
For industries where calling drives revenue, reducing machine-handled time makes operations cleaner.
Omnichannel alternatives to hidden calls
Repeated outbound calls from masked numbers erode trust. Many customers prefer other channels when they’re available.
Messaging has become a primary way for a large share of users to interact with businesses. Surveys consistently show most customers want to engage through their preferred messaging channel.
Offering alternatives like:
- WhatsApp Business
- SMS follow-up
- Webchat
- Social messaging channels
reduces the need for repeated outbound voice attempts.
Instead of piling up call volume, teams can shift to verified digital conversations within a unified workspace. This gives clearer identity context and a documented interaction history.
The goal: fewer unnecessary anonymous touchpoints.
Smart call routing and call screening
On the inbound side, risk reduction starts with structured routing.
Flow-based screening lets organizations define how anonymous or withheld calls enter the system. Using rule-based IVR configuration, teams can:
- Route calls through predefined menus.
- Require DTMF input before agent connection.
- Send certain traffic to voicemail.
- Separate anonymous calls into dedicated queues.
This is predefined logic, not real-time interpretation. It makes sure inbound traffic follows controlled paths before reaching live agents.
Secure data handling stays separate from caller identity. Payment capture, recording controls, and data visibility policies run according to internal configuration, regardless of whether a number is displayed.
The result: controlled visibility into how each call is handled.
Explore how Voiso helps businesses manage anonymous inbound calls securely.
FAQs
Can you call back a No Caller ID number?
No. If the caller suppressed their number, your device didn’t receive a returnable contact. In some regions, carrier call return codes may try to reconnect the last incoming call, but results vary. There’s no reliable consumer method to directly reveal or redial a withheld number.
Is it legal to trace a private number?
Tracing is legal only through regulated channels. Carriers may support call trace services for harassment or fraud cases. Subscriber details are typically released only to law enforcement under formal request. Trying to bypass carrier systems with third-party “unmasking” tools can create legal and privacy risks.
What’s the difference between No Caller ID and Unknown Caller?
“No Caller ID” usually means the caller intentionally suppressed their CLI. “Unknown Caller” typically shows up when the network couldn’t deliver a number due to routing or signaling issues. In both cases, your device has no usable number to call back.
Are apps that reveal private numbers safe?
Apps can’t retrieve a number that was never transmitted to your device. Most rely on crowdsourced databases or reverse lookup services, which only work when a number exists. Services promising instant unmasking should be treated with caution, especially if they ask for payment or personal information.
Why would a legitimate company hide their number?
Organizations often mask outbound calls to centralize callbacks, protect staff identities, or keep routing within monitored systems. This is common in financial services, healthcare, and contact centers. A withheld number on its own doesn’t mean anything malicious is happening.
Can contact center software identify anonymous callers?
Contact center platforms may log structured metadata like timestamps, routing paths, and call outcomes, even when caller ID is withheld. But if the originating number isn’t transmitted through the network, the system can’t independently “unmask” the caller. What’s visible depends on carrier signaling and configuration.